The Cyber Resilience Act: Why It Matters to You
Table of contents
If you have some technical interest, you might have heard about the EU’s Cyber Resilience Act. No matter whether you are an end user, manufacturer, developer, importer, or distributor of a so-called product with digital elements1 on the EU market, the CRA will impact you. As an increasing share of products we buy are products with digital elements, which include smart door locks, Wi-Fi routers, connected washing machines, mobile apps or computer games, virtually anyone will be impacted. But what does this mean and why should you care?
The Problem
Not only are the products we personally buy increasingly digitalised and connected, but our society and its infrastructure follows the same trend. This has turned into a reliance on digital products and services that is regularly highlighted when there are major internet service outages that can impact services like emergency calls, transport infrastructure or grocery stores.
While mass outages make headlines, the underlying problem is more pervasive: our digital infrastructure is brittle. Vulnerabilities in products with digital elements are not just technical bugs but also real-world risks. A flaw in a smart door lock can become a physical security breach, a vulnerability in a Wi-Fi router can serve as an entry point for ransomware that paralyzes a business, a bug in an industrial controller can disrupt energy supplies. We are building our infrastructure on insecure building blocks that are increasingly under attack.
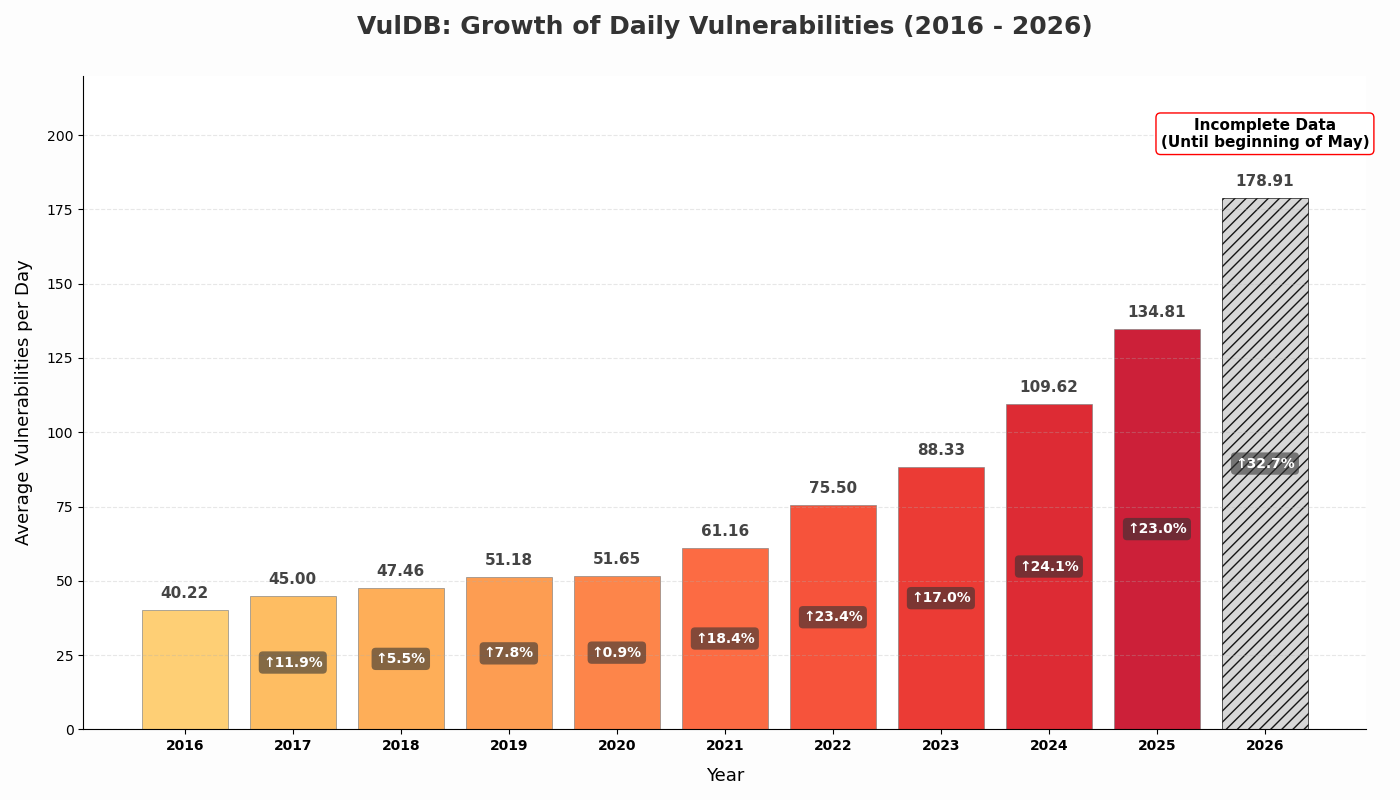
Growth of daily vulnerability entries (2016–2026), highlighting the increasing scale of the security challenges (data from VulDB).
If we take a look at statistics of the average number of new vulnerability entries added per day to VulDB “the number 1 vulnerability database documenting more than 362000 vulnerabilities since 1970”, we see a steep, accelerating curve. This acceleration does not necessarily mean that software is getting worse. Instead, it is the consequence of the growing amount of software being used that is increasingly complex and connected. Additionally, the tools that help us find vulnerabilities are getting better and AI accelerates this trend. These tools, however, are available to both defenders and attackers. The severity of this situation is shown in the graph below from Zero Day Clock.
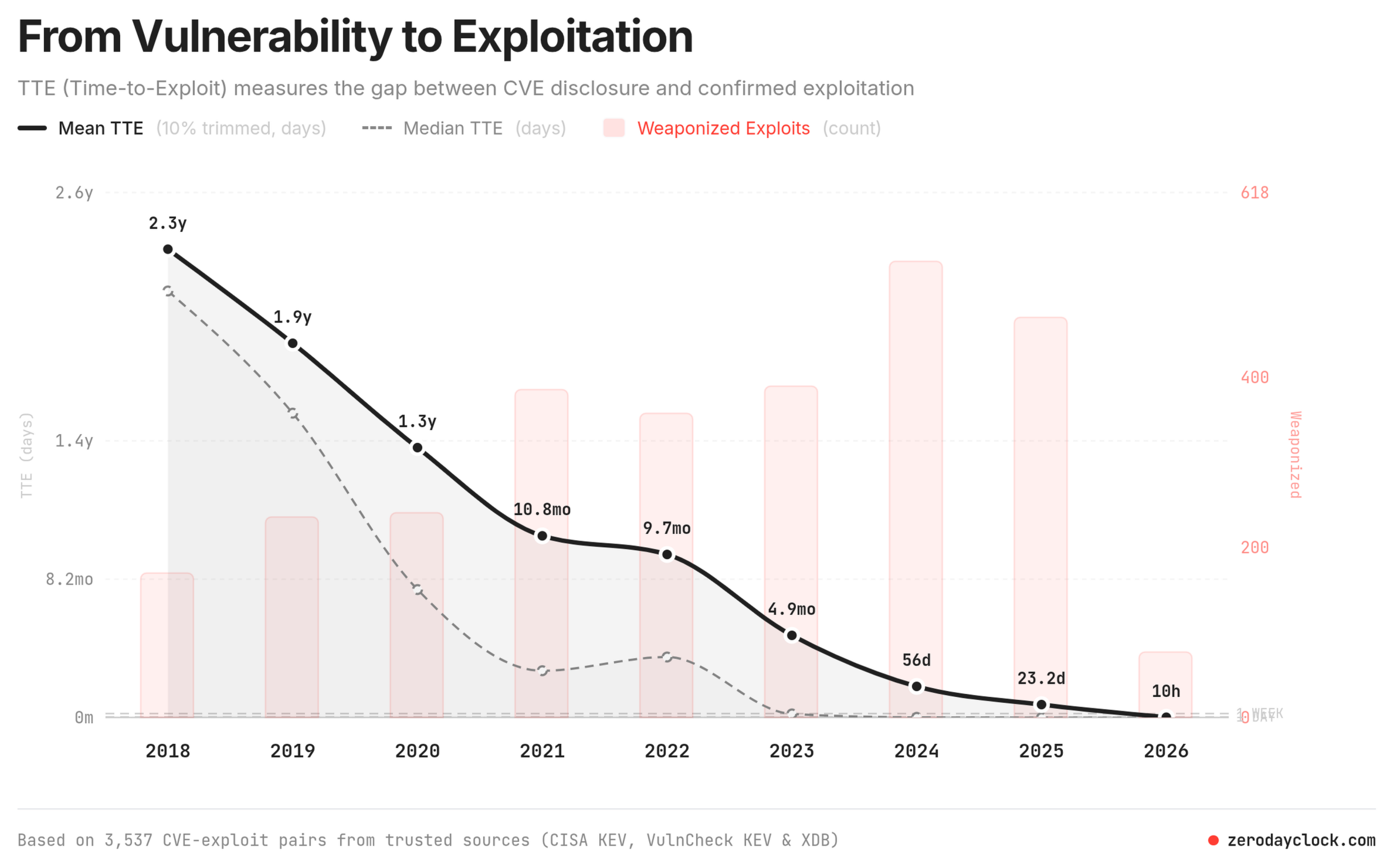
The trend of Time-to-Exploit (TTE), showing the drastic reduction in the time it takes for a vulnerability to be exploited (graph from Zero Day Clock).
When looking at vulnerabilities that are confirmed exploited (ca. 1 to 2,2 % of all disclosed vulnerabilities), the Time-to-Exploit, i.e., the time it takes between a disclosed vulnerability and a confirmed exploit has gone from over a year in 2020 to under 12 hours at the beginning of May 2026. The researchers behind Zero Day Clock, which are supported by numerous experts of the cybersecurity industry, currently project the Time-to-Exploit will reach 1 hour later during 2026 and 1 minute by around 2028.
While this projection looks alarming, we have the possibility to act and make sure that the time to remediate vulnerabilities follows the same trend. We can see this as a motivation for ensuring that our digital infrastructure reaches a mature level of cybersecurity.
It is important to acknowledge that there will never be perfect cybersecurity, and this is not the aim when designing secure products and systems. Instead, we need to understand in what way attackers threaten our systems, what a successful attack means to users as well as connected systems, and how feasible a certain attack is. With this understanding, we can apply the mitigations and processes required to manage cybersecurity risks. This shifts the focus towards resilience, the system’s ability to anticipate, withstand, and adapt to adverse conditions or attacks in order to maintain essential functions.
The Answer
This is where the EU’s Cyber Resilience Act (CRA) comes in, a legal framework designed to ensure that products with digital elements are developed with security as a primary consideration rather than an afterthought. Mandatory vulnerability and incident reporting will come into force on 11th September 2026, with full enforcement following on 11th December 2027.
The CRA, and the standards which help us follow this legislation, push the industry towards a risk-based approach to cybersecurity. This is a fundamentally different approach compared to previous legislation like the cybersecurity requirements of the Radio Equipment Directive2, which was rather an implementation checklist. In contrast, CRA takes a product’s intended purpose or reasonably foreseeable use into account, and applies requirements proportional to the cybersecurity risks identified during a risk assessment.
In essence, CRA aims for resilience using three core concepts3:
- Security by Design: Integrating cybersecurity from the early stages of a product lifecycle instead of treating it as an afterthought.
- Secure by Default: Ensuring the product leaves the factory with secure defaults for the intended purpose and operational environment, where features that introduce increased risk need to be enabled by an informed user. This includes installing cybersecurity updates without undue delay.
- Transparency: Creating a culture of open communication, where relevant stakeholders are provided with the necessary information for achieving and maintaining the cybersecurity of the products.
The Impact
The immediate impact of the CRA will be felt by companies developing products with digital elements, who have to modernize their development processes. Security can no longer be treated as a checklist towards the end of a project but needs to be integrated into the product lifecycle from the early concept to decommissioning. This involves, e.g., an investment in rigorous risk assessments, threat modelling, and a clear understanding of when risks can be accepted.
This modernization is not optional, but ensured with severe fines of up to EUR 15 000 000 or 2,5% of the company’s total worldwide annual turnover when the “essential cybersecurity requirements” are not followed. Even providing incorrect, incomplete or misleading information to notified bodies and market surveillance authorities can lead to fines of up to EUR 5 000 000 or 1% of the company’s total worldwide annual turnover. Not following CRA becomes a critical legal and financial risk.
Economically, the incentive for manufacturers is a double-edged sword. On one hand, the EU estimates that this initiative could reduce the cost of incidents affecting businesses by roughly EUR 180 to 290 billion annually4. On the other hand, the direct compliance costs are estimated to up to EUR 29 billion, for fulfilling the new requirements and documentation. Furthermore, there is a historical tension in the industry: security is sometimes seen as a barrier to rapid development and market entry, leading some companies to prioritize speed-to-market over robustness5. The cost of lacking cybersecurity is today often carried by the end user, however. By mandating a horizontal framework, the CRA aims to correct these “market imperfections” and prevent that less secure products drive out the secure ones due to lower costs.
Will It Work?
Technology is often seen as a cure-all these days, especially when AI is involved. From this point of view, it might be hard to accept that the Cyber Resilience Act (CRA) can be a significant piece of the puzzle to secure our infrastructure and digital lives, instead of just another regulatory burden.
To me, it is clear that the economic incentives for building secure products need fixing. We cannot allow less secure products to out-compete those that prioritize security. This should not mean, however, that regulatory burdens stifle innovation. Therefore, the CRA does not simply mandate a rigid checklist of cybersecurity controls. Instead, it pushes the industry towards a risk-based approach, ensuring that requirements are proportionate to the risks faced and the product’s intended purpose.
You cannot simply claim to have low cybersecurity risks, you must demonstrate it. This is where I see a need for the development of new methods and tooling. Today, it is particularly difficult for small and medium-sized enterprises (SMEs) to get started and accurately understand the risks associated with their products.
The second challenge is the operational burden of implementing vulnerability management. I view this not as a hurdle, but as a modernization of development processes, similar to the introduction of CI/CD pipelines. It creates a clear interface to the risk management that a company must perform for other operational risks anyway.
Of course, the road to compliance will not be seamless. Transitioning to a risk-based model requires a fundamental shift in how we build software, and there is a real risk that companies focus more on documenting compliance than on actually improving security. To prevent this, there is a need for the security community to translate these high-level legal requirements into practical, actionable engineering patterns. The success of the CRA depends not just on the legislation itself, but on our ability to make the path to security accessible and implementable for developers of all levels.
While the start may be rough and stressful, the long-term outlook is promising. The CRA addresses two primary market failures: a general low level of cybersecurity characterized by widespread vulnerabilities and inconsistent updates, and a lack of transparency that prevents users from making informed security choices. By establishing a coherent framework and a level playing field, the EU aims to increase trust among users and ensure security is handled seriously throughout a product’s entire lifecycle.
Ultimately, this shift will lead to maturer development processes and higher-quality products. By moving away from a fragmented landscape of diverging national rules, we can create a digital society where security is not a luxury or a competitive disadvantage, but a fundamental standard.
-
As defined in Article 3 of the CRA: ‘product with digital elements’ means a software or hardware product and its remote data processing solutions, including software or hardware components being placed on the market separately ↩︎
-
Commission Delegated Regulation (EU) 2022/30 to be precise. ↩︎
-
These concepts including the risk-based approach to cybersecurity are defined in the “horizontal” CRA standard EN 40000-1-2, which is available as a mature draft at the time of this writing. ↩︎
-
Why Information Security is Hard – An Economic Perspective; Ross Anderson, University of Cambridge ↩︎